What is a pentest?
In a pentest, ethical hackers simulate an attack on an organization to identify risks. This makes pentesting part of a complete security strategy.
In a pentest, ethical hackers simulate an attack on an organization to identify risks. This makes pentesting part of a complete security strategy.
A penetration test (pentest,) is a simulated attack on a computer system to evaluate its security. Pentesters use the tools, techniques and processes that a malicious attacker would deploy to find and demonstrate the effects of weaknesses in a system. A pentest simulates various tactics and techniques that could threaten an organization. This examines a system's ability to withstand sophisticated attacks from authenticated and unauthenticated positions. With an appropriate scope, a pen test can basically assess the security of any aspect of a system.
Applications and systems should be designed in a way that minimizes the risk of security breaches. A pen test provides insight into how well that goal has been achieved. On this basis, conducting (or having conducted) a pen test can help organizations with:
Don't hesitate to contact us; we would be happy to tell you more about everything concerning Cybersecurity.

It is best to have a pen test performed by someone with little to no prior knowledge of how the system is secured because they can uncover blind spots that have been overlooked by the developers who built the system. For this reason, outside contractors are usually hired to conduct the tests. These contractors are often called "ethical hackers" because they are hired to break into a system with permission and for the purpose of improving security.
Many ethical hackers are experienced developers with advanced degrees and certification in pen testing. On the other hand, some of the best ethical hackers are self-taught. Some are even reformed criminal hackers who now use their expertise to fix security vulnerabilities rather than exploit them. The best candidate to perform a pen test can vary greatly depending on the target company and the type of pen test they want to perform.
A pen test provides insight into the most vulnerable aspects of a system. It also serves as a preventive security analysis, allowing organizations to fix discovered vulnerabilities before potential attackers can exploit them.
Here are four reasons why organizations should conduct pen tests:
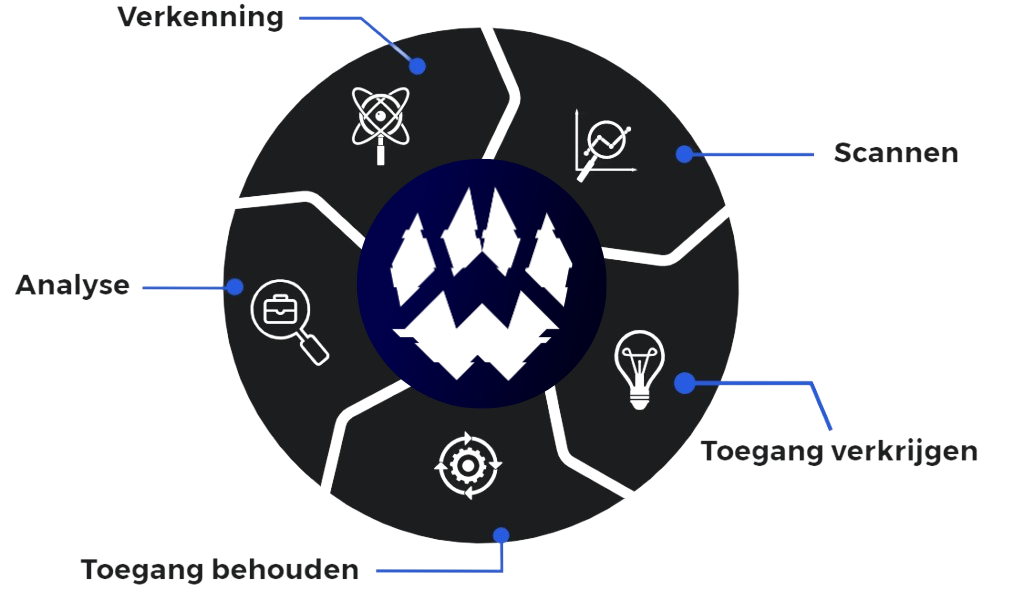
A pen test simulates attacks by motivated adversaries. To do this, testers usually follow a plan that includes the following steps:
Depending on the objectives of a pen test, testers are given varying degrees of information about or access to the target system. In some cases, the pentest team chooses one approach at first and stays with it. In other cases, the test team develops its strategy as knowledge of the system increases during the pen test. There are three levels of access for a pen test:
a total lack of information: In a black box pen test, the tester receives no information at all. In this case, the pentester follows the approach of an unauthorized attacker, from initial access and execution to exploitation. This scenario can be seen as the most authentic, showing how an adversary would attack and compromise an organization without prior knowledge.
Grey box: In a grey box pen test, only limited information is shared with the tester. Usually this is in the form of login credentials. Grey box tests are useful for understanding the degree of access a privileged user could have and the potential damage they could cause. Grey box tests balance depth and efficiency and can be used to simulate an insider threat or an attack through the network perimeter.
White box: In a white box pen test, complete network and system information is shared with the tester, including network maps and credentials. This helps save time and reduce the overall cost of a job. A white box pen test is useful for simulating a targeted attack on a specific system using as many attack vectors as possible.
A thorough approach to Cybersecurity is essential for optimal risk management. This includes having all systems and applications that are potential targets for attackers tested.
How often pen tests should be performed depends on many factors, but most security experts recommend doing it at least once a year because it can detect emerging vulnerabilities, such as zero-day threats. According to Google at least 41 zero-day threats had surfaced by 2022.
Organizations should consider the following factors when planning pen tests:
In addition to regularly scheduled pen tests, organizations should also conduct security tests when the following events occur:
After the successful completion of a pen test, an ethical hacker shares his findings with the target organization's information security team. Ethical hackers usually categorize their findings with a score based on severity, so the issues with the highest score are prioritized for remediation.
The organization uses these findings as the basis for further investigation, assessment and security remediation. Decision makers and stakeholders are also involved at this stage, and the organization's IT or security team makes deadlines to ensure that all security issues are addressed quickly.
Pentesting is unique from other cybersecurity assessment methods because it can be adapted to any industry or organization. Depending on an organization's infrastructure and operations, a particular set of hacking techniques or tools may be required. These techniques and their methodologies may also vary based on IT personnel and their company standards. Using the following customizable six-step process, pen tests provide a range of results that can help organizations proactively update their measures:
Pentesters use a number of tools to perform reconnaissance, detect vulnerabilities and automate certain parts of the pen test. Some of the most commonly used tools are:
Specialized control systems: Most pentesters use operating systems designed for pen testing and ethical hacking. The most popular is Kali Linux, an open-source Linux distribution that comes with pentesting tools such as Nmap, Wireshark and Metasploit.
Tools for cracking credentials: These programs can recover passwords by breaking encryptions or performing brute-force attacks, using bots or scripts to automatically generate possible passwords and test them until one works. Examples include Medusa, Hydra, Hashcat and John the Ripper.
Gate scanners: Port scanners allow remote pentesters to test devices for open and available ports, which they can use to penetrate a network. Nmap is the most commonly used port scanner, but masscan and ZMap are also common.
Vulnerability scanners: Vulnerability scanning tools search systems for known vulnerabilities, allowing pentesters to quickly find potential entries into a target. Examples include Nessus, Core Impact and Netsparker.
Web vulnerability scanners are a subset of vulnerability scanners that assess Web applications and Web sites. Examples include Burp Suite and OWASP's Zed Attack Proxy (ZAP).
Packet analyzers: packet analyzers, also called packet sniffers, allow pentesters to analyze network traffic by capturing and inspecting packets. Pentesters can find out where traffic comes from, where it goes and - in some cases - what data it contains. Wireshark and tcpdump are among the most widely used packet analyzers.
Metasploit: Metasploit is a framework for pentesting with a host of features. Most importantly, Metasploit allows pentesters to automate cyber attacks. Metasploit has a built-in library of pre-written exploit codes and payloads. Pentesters can select an exploit, give it a payload to deliver to the target system and let Metasploit handle the rest.
Although a pen test is largely performed manually, pentesters also use automated scanning and testing tools. But they also go beyond these tools, using their knowledge of the latest attack techniques to perform more in-depth testing than a vulnerability assessment (or automated testing).
Manual pen tests uncover vulnerabilities and weaknesses that are not in popular lists (e.g.. OWASP Top 10) and tests business logic that automated tests may overlook (e.g., data validation, integrity checking). A manual pentest can also help identify false positives reported by automated tests. Because pentesters are experts who think like adversaries, they can analyze data to target their attacks and test systems and Web sites in a way that automated testing solutions that follow a scripted routine cannot.
Automated testing generates results faster and requires fewer specialized professionals than a fully manual pen testing process. Tools for automated testing track results automatically and can sometimes export them to a centralized reporting platform. Also, the results of manual pen testing can vary from test to test, while repeatedly running automated tests on the same system produces the same results.
With the frequency and severity of security breaches increasing year after year, organizations have never needed more insight into how to resist attacks. In addition, various regulations and security standards such as the AVG and ISO 27001 require an organization to have its security tested on a regular basis. With these needs in mind, here are some pros and cons of this type of security testing.